Luxembourg ID Card
The Luxembourg ID container facilitates communication with card readers with inserted Luxembourg ID smart card. The T1C-JLIB client library provides function to communicate with the smart card and facilitates integration into a native or Java application. This document describes the functionality provided by the Luxembourg ID container on the T1C-GCL (Generic Connector Library).
Get Luxembourg ID container object
For more information on how to configure the T1C-JLIB client library see Client Configuration.
Initialize a T1cClient:
LibConfig conf = new LibConfig();
conf.setEnvironment(Environment.DEV);
conf.setDsUri(DS_URI);
conf.setOcvUri(OCV_URI);
conf.setGclClientUri(URI_T1C_GCL);
conf.setApiKey(API_KEY);
conf.setHardwarePinPadForced(false);
conf.setDefaultPollingIntervalInSeconds(5);
conf.setDefaultPollingTimeoutInSeconds(10);
conf.setSessionTimeout(60);
T1cClient t1cClient = new T1cClient(conf);
Get the Luxembourg ID container service:
LuxIdContainer container = t1cClient.getLuxIdContainer(reader, "123456");
Note that we pass both the reader object and pin code in this call. Unlike other cards, all communication with the Luxembourg ID card is protected with the PIN code.
For demonstration purpose we will use the aforementioned callback, which only outputs the data and eventual error messages. During integration meaningful functionality should be provided.
The pin should be provided in order to instantiate the container. Providing the PIN at instantiation of the container, means that the PIN will be stored in the container object - but not persisted - for the lifetime of the container instance.
Obtain the GclReader object
The constructor for the Luxembourg ID expects a GclReader object and a String PIN as parameters. A GclReader can be obtained from the exposed core functionality, for more information see Core Services.
Core services responds with available card-readers, available card in a card-reader, etc.
For example:
In order to get all connected card-readers, with available cards:
List<GclReader> reader = t1cClient.getCore().getReadersWithInsertedCard();
This function call returns a list of the following objects:
com.t1t.t1c.GclReader
| Name | Description | Example Value | Type |
|---|---|---|---|
id |
The reader ID | "57a3e2e71c48cee9" | java.lang.String |
name |
The reader name | "Bit4Id miniLector" | java.lang.String |
pinpad |
The presence of a hardware PIN-pad | false | java.lang.Boolean |
card |
The inserted card | see below | com.t1t.t1c.core.GclCard |
com.t1t.t1c.GclCard
| Name | Description | Example Value | Type |
|---|---|---|---|
atr |
Answer to Reset | "3B9813400AA503010101AD1311" | java.lang.String |
description |
List of descriptions | ["Belgium Electronic ID Card"] | java.util.List<java.lang.String> |
We notice that a card object is available in the response in the context of a detected reader.
The reader in the example above is Bit4id miniLector, has no pin-pad capabilities, and there is a card detected with given ATR and description "Grand Duchy of Luxembourg...".
An ATR (Answer To Reset) identifies the type of a smart-card.
The reader, has a unique ID, id; this id must be used in order to request functionalities for the Luxembourg eID card.
The container must be instantiated with the GclReader object containing the Luxembourg eID card and its PIN:
LuxIdContainer container = t1cClient.getLuxIdContainer(reader.getId(), "123456");
All methods for container will use the selected reader - identified by the reader object.
Cardholder Information
The card holder is the person identified using the Luxembourg eID card. It's important to note that all data must be validated in your backend. Data validation can be done using the appropriate certificate (public key).
Biometric Information
Contains all biometric related data, excluding the card holder address and picture.
The service can be called:
GclLuxIdBiometric biometric = container.getBiometric();
Response:
com.t1t.t1c.containers.smartcards.eid.lux.GclLuxIdBiometric
| Name | Description | Example Value | Type |
|---|---|---|---|
birthDate |
The birthdate | "830819" | java.lang.String |
documentNumber |
The document number | "SPEC04168" | java.lang.String |
documentType |
The document type | "ID" | java.lang.String |
firstName |
The first name | "SPECIMEN" | java.lang.String |
gender |
The gender | "F" | java.lang.String |
issuingState |
The issuing state | "LUX" | java.lang.String |
lastName |
The last name | "SPECIMEN" | java.lang.String |
nationality |
The nationality | "LUX" | java.lang.String |
validityEndDate |
The card validity end date | "251116" | java.lang.String |
validityStartDate |
The card validity start date | "151116" | java.lang.String |
rawData |
The raw data | "830819" | java.lang.String |
Picture
Contains the card holder's picture stored on the smart card. The service can be called:
GclLuxIdPicture picture = container.getPicture();
Response:
com.t1t.t1c.containers.smartcards.eid.lux.GclLuxIdPicture
| Name | Description | Example Value | Type |
|---|---|---|---|
height |
The picture height | 320 | java.lang.Integer |
width |
The picture width | 240 | java.lang.Integer |
image |
The base64 image | "/0//UQAvAAAAAADwAAABQAAAAAAAAAAAAAAA8AAA....uq9eK159DRO61Ufrf9ICA/9k=" | java.lang.String |
rawData |
The raw data | "dYIljn9hgiWJAgEBf2CCJYGhD4AC....IACF8ugiVrRkFDADAxMAAAACVrAAEA" | java.lang.String |
Signature Image
Contains the card holder's signature image stored on the smart card. The service can be called:
GclLuxIdSignatureImage picture = container.getSignatureImage();
Response:
com.t1t.t1c.containers.smartcards.eid.lux.GclLuxIdSignatureImage
| Name | Description | Example Value | Type |
|---|---|---|---|
image |
The base64 image | "/0//UQAvAAAAAADwAAABQAAAAAAAAAAAAAAA8AAA....uq9eK159DRO61Ufrf9ICA/9k=" | java.lang.String |
rawData |
The raw data | "dYIljn9hgiWJAgEBf2CCJYGhD4AC....IACF8ugiVrRkFDADAxMAAAACVrAAEA" | java.lang.String |
Certificates
Exposes all the certificates publicly available on the smart card. The following certificates can be found on the card:
- Root certificate
- Intermediate certificate
- Authentication certificate
- Non-repudiation certificate
T1C-JLIB will return the raw base64 certificate, optionally it can also return an java.securtity.Certificate object representing the certificate. To enable parsing, parseCerts must be set to true.
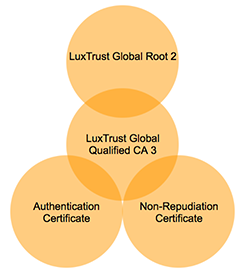
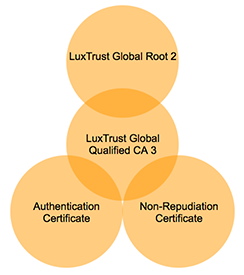
The root and intermediate certificates are both stored as root certificates.
Certificate Chain
Root Certificates
Contains the 'root certificate' stored on the smart card. The root certificate is used to sign the 'intermediate certificate'.
The service can be called:
List<T1cCertificate> rootCertificates = container.getRootCertificates(true);
Response:
java.util.List<com.t1t.t1c.model.T1cCertificate>
| Name | Description | Example Value | Type |
|---|---|---|---|
base64 |
The base64 encoded certificate | ""MIIFjjCCA3agAwI...rTBDdrlEWVaLrY+M+xeIctrC0WnP7u4xg==" | java.lang.String |
parsed |
The decoded certificate | N/A | java.security.cert.Certificate |
There are 2 root certificates on the card, one is the issuer certificate of the intermediate
Authentication Certificate
Contains the 'authentication certificate' stored on the smart card. The 'authentication certificate' contains the public key corresponding to the private RSA authentication key. The 'authentication certificate' is needed for pin validation, authentication and singing.
The service can be called:
T1cCertificate authenticationCertificate = container.getAuthenticationCertificate(true);
Response:
com.t1t.t1c.model.T1cCertificate
| Name | Description | Example Value | Type |
|---|---|---|---|
base64 |
The base64 encoded certificate | ""MIIFjjCCA3agAwI...rTBDdrlEWVaLrY+M+xeIctrC0WnP7u4xg==" | java.lang.String |
parsed |
The decoded certificate | N/A | java.security.cert.Certificate |
Non-repudiation Certificate
Contains the 'non-repudiation certificate' stored on the smart card. The 'non-repudiation certificate' contains the public key corresponding the private RSA non-repudiation key.
The service can be called:
T1cCertificate nonRepudiationCertificate = container.getNonRepudiationCertificate(true);
Response:
com.t1t.t1c.model.T1cCertificate
| Name | Description | Example Value | Type |
|---|---|---|---|
base64 |
The base64 encoded certificate | ""MIIFjjCCA3agAwI...rTBDdrlEWVaLrY+M+xeIctrC0WnP7u4xg==" | java.lang.String |
parsed |
The decoded certificate | N/A | java.security.cert.Certificate |
Data Filter
Filter Card Holder Information
All data on the smart card can be dumped at once, or using a filter. In order to read all data at once:
LuxIdAllData data = container.getAllData();
Response:
com.t1t.t1c.containers.smartcards.eid.lux.LuxIdAllData
| Name | Description | Example Value | Type |
|---|---|---|---|
biometric |
The biometric data | See above | com.t1t.t1c.containers.smartcards.eid.lux.GclLuxIdBiometric |
signatureImage |
The signature image | See above | com.t1t.t1c.containers.smartcards.eid.lux.GclLuxIdSignatureImage |
signatureObject |
The signature object | See above | java.lang.String |
picture |
The picture | See above | com.t1t.t1c.containers.smartcards.eid.lux.GclLuxIdPicture |
rootCertificates |
The root certificates | See above | java.util.List<com.t1t.t1c.model.T1cCertificate> |
authenticationCertificate |
The RN data | See above | com.t1t.t1c.model.T1cCertificate |
nonRepudiationCertificate |
The root certificate | See above | com.t1t.t1c.model.T1cCertificate |
The filter can be used to ask a list of custom data containers. For example, we want to read only the 'biometric', and 'authentication certificate':
// filter entries := ["authentication-certificate","biometric","non-repudiation-certificate","picture","root-certificates"]
List<String> filters = Arrays.asList("biometric","authentication-certificate");
boolean parseCertificates = true;
LuxIdAllData data = container.getAllData(filters, parseCertificates);
Filter Certificates
All certificates on the smart card can be dumped at once, or using a filter. In order to read all certificates at once:
LuxIdAllCertificates certificates = container.getAllCertificates();
Response:
com.t1t.t1c.containers.smartcards.eid.lux.LuxIdAllData
| Name | Description | Example Value | Type |
|---|---|---|---|
rootCertificates |
The root certificates | See above | java.util.List<com.t1t.t1c.model.T1cCertificate> |
authenticationCertificate |
The RN data | See above | com.t1t.t1c.model.T1cCertificate |
nonRepudiationCertificate |
The root certificate | See above | com.t1t.t1c.model.T1cCertificate |
The filter can be used to ask a list of custom data containers. For example, we want to read only the 'authentication-certificate':
// filter entries := ["authentication-certificate","non-repudiation-certificate","root-certificates"];
List<String> filters = Arrays.asList("authentication-certificate");
boolean parseCertificates = true;
LuxIdAllCertificates certificates = container.getAllCertificates(filters, parseCertificate);
Sign Data
Data can be signed using the Luxembourg ID smart card. To do so, the T1C-GCL facilitates in:
- Retrieving the certificate chain (root, inetermediate and non-repudiation certificate)
- Perform a sign operation (private key stays on the smart card)
- Return the signed hash
To get the certificates necessary for signature validation in your back-end:
List<String> filters = Arrays.asList("root-certificates","authentication-certificate","non-repudiaton-certificate");
boolean parseCertificates = false;
LuxIdAllCertificates certificates = container.getAllCertificates(filters, parseCertificate);
// Or directly retrieve the signing certificate chain in the form of Map<Integer, T1cCertificate>. The leaf certificate will always have 0 as key
Map<Integer, T1cCertificate> signingCertificateChain = container.getSigningCertificateChain();
Depending on the connected smart card reader, a sign can be executed in 2 modes:
- Using a connected card reader with 'pin-pad' capabilities (keypad and display available)
- Using a connected card reader without 'pin-pad' capabilities (no keypad nor display available)
Security consideration: In order to sign a hash, security considerations prefer using a 'pin-pad'.
Sign Hash
When the native or Java application is responsible for showing the password input, the following request is used to sign a given hash:
String signedData = container.sign(
//data
"I2e+u/sgy7fYgh+DWA0p2jzXQ7E=",
//Digest algorithn
DigestAlgorithm.SHA256,
//Optional PIN
"1234"
);
Response is a base64 encoded signed hash:
"W7wqvWA8m9SBALZPxN0qUCZfB1O/WLaM/silenLzSXXmeR+0nzB7hXC/Lc/fMru82m/AAqCuGTYMPKcIpQG6MtZ/SGVpZUA/71jv3D9CatmGYGZc52cpcb7cqOVT7EmhrMtwo/jyUbi/Dy5c8G05owkbgx6QxnLEuTLkfoqsW9Q="
The 'algorithmReference' property can contain the following values: SHA1, SHA256, SHA512, MD5.
Avoid using SHA-1: it is deprecated on the interface and will not be available in the future
Calculate Hash
In order to calculate a hash from the data to sign, you need to know the algorithm you will use in order to sign.
You might have noticed the algorithmReference property provided in the sign request.
The algorithmReference can be one of the values: MD5, SHA1, SHA256, SHA512.
For example, we want the following text to be signed using SHA256:
This is sample text to demonstrate siging with Luxembourg eID
You can use the following online tool to calculate the SHA256: calculate SHA256
Hexadecimal result:
135b870026cfbe12dec348069811fcde5bed28800ac54dbf45ecdf04eb13e95b
Notice that the length of the SHA256 is always the same.
Now we need to convert the hexadecimal string to a base64-encoded string, another online tool can be used for this example: hex to base64 converter
Base64-encoded result:
E1uHACbPvhLew0gGmBH83lvtKIAKxU2/RezfBOsT6Vs=
Now we can sign the data:
String signedData = container.sign(
//data
"E1uHACbPvhLew0gGmBH83lvtKIAKxU2/RezfBOsT6Vs=",
//Digest algorithn
DigestAlgorithm.SHA256,
//Optional PIN
"1234"
);
Result:
"C7SG5eix1+lzMcZXgL0bCL+rLxKhd8ngrSj6mvlgooWH7CloEU13Rj8QiQHdhHnZgAi4Q0fCMIqAc4dn9uW9OP+MRitimRpYZcaDsGrUehPi/JpOD1e+ko7xKZ67ijUU4KTmG4HXc114oJ7xxx3CGL7TNFfvuEphLbbZa+9IZSSnYDOOENJqhggqqu7paSbLJrxC2zaeMxODKb5WSexHnZH6NnLPl2OmvPTYtxiTUMrLbFRsDRAziF6/VQkgM8/xOm+1/9Expv5DSLRY8RQ+wha6/nMlJjx50JszYIj2aBQKp4AOxPVdPewVGEWF4NF9ffrPLrOA2v2d7t5M4q7yxA==",
Verify PIN
Verify PIN without pin-pad
When the native or Java application is responsible for showing the password input, the following request is used to verify a card holder PIN:
Boolean pinVerified = container.verifyPin("123456");
Response:
java.lang.Boolean
Verify PIN - retries left
In order to inform a user upon the PIN retries left, the Luxembourg eID doesn't provide a request to retrieve this information. After an unsuccessful PIN verification, the error code indicates the number of retries left. For example, when executing:
Boolean pinVerified = container.verifyPin("132567");
The following exception will be thrown when PIN is wrong:
com.t1t.t1c.exceptions.VerifyPinException
| Name | Description | Example Value | Type |
|---|---|---|---|
message |
The message | "Wrong pin, 2 tries remaining" | java.lang.String |
retriesLeft |
The amount of retries left | 2 | java.lang.Integer |
Note that, when the user has at least one retry left,entering a correct PIN resets the PIN retry status.
Authentication
The T1C-GCL is able to authenticate a card holder based on a challenge. The challenge can be:
- provided by an external service
- provided by the smart card
An authentication can be interpreted as a signature use case, the challenge is signed data, that can be validated in a back-end process.
To get the certificates necessary for signature validation in your back-end:
Map<Integer, T1cCertificate> signingCertificateChain = container.getAuthenticationCertificateChain();
External Challenge
An external challenge is provided in the data property of the following example:
String authenticatedData = container.authenticate(
//data
"E1uHACbPvhLew0gGmBH83lvtKIAKxU2/RezfBOsT6Vs=",
//Digest algorithn
DigestAlgorithm.SHA256,
//Optional PIN
"1234"
);
Response:
"W7wqvWA8m9SBALZPxN0qUCZfB1O/WLaM/silenLzSXXmeR+0nzB7hXC/Lc/fMru82m/AAqCuGTYMPKcIpQG6MtZ/SGVpZUA/71jv3D9CatmGYGZc52cpcb7cqOVT7EmhrMtwo/jyUbi/Dy5c8G05owkbgx6QxnLEuTLkfoqsW9Q="
Take notice that the PIN property can be omitted when using a smart card reader with pin-pad capabilities. The 'algorithmReference' property can contain the following values: SHA1, SHA256, SHA512, MD5.
Generated Challenge
A server generated challenge can be provided to the Java library. In order to do so, an additional contract must be provided with the 'OCV API' (Open Certificate Validation API).